- If Citrix Receiver is already installed, click ‘Already Installed’ Most managed systems will have a pre-installed Citrix Receiver, and you may ignore the license agreement at this time If your system does not have Citrix Receiver, you may accept the agreement, and proceed with a manual installation.
- Citrix Single Sign-On (SSONSVR.exe) Fails to Start on computers using Intel Credentials Manager.
- Single Sign On Solutions
- Citrix Network Provider Order
- Citrix Receiver Single Sign On Command Line
- Citrix Receiver Enable Single Sign On
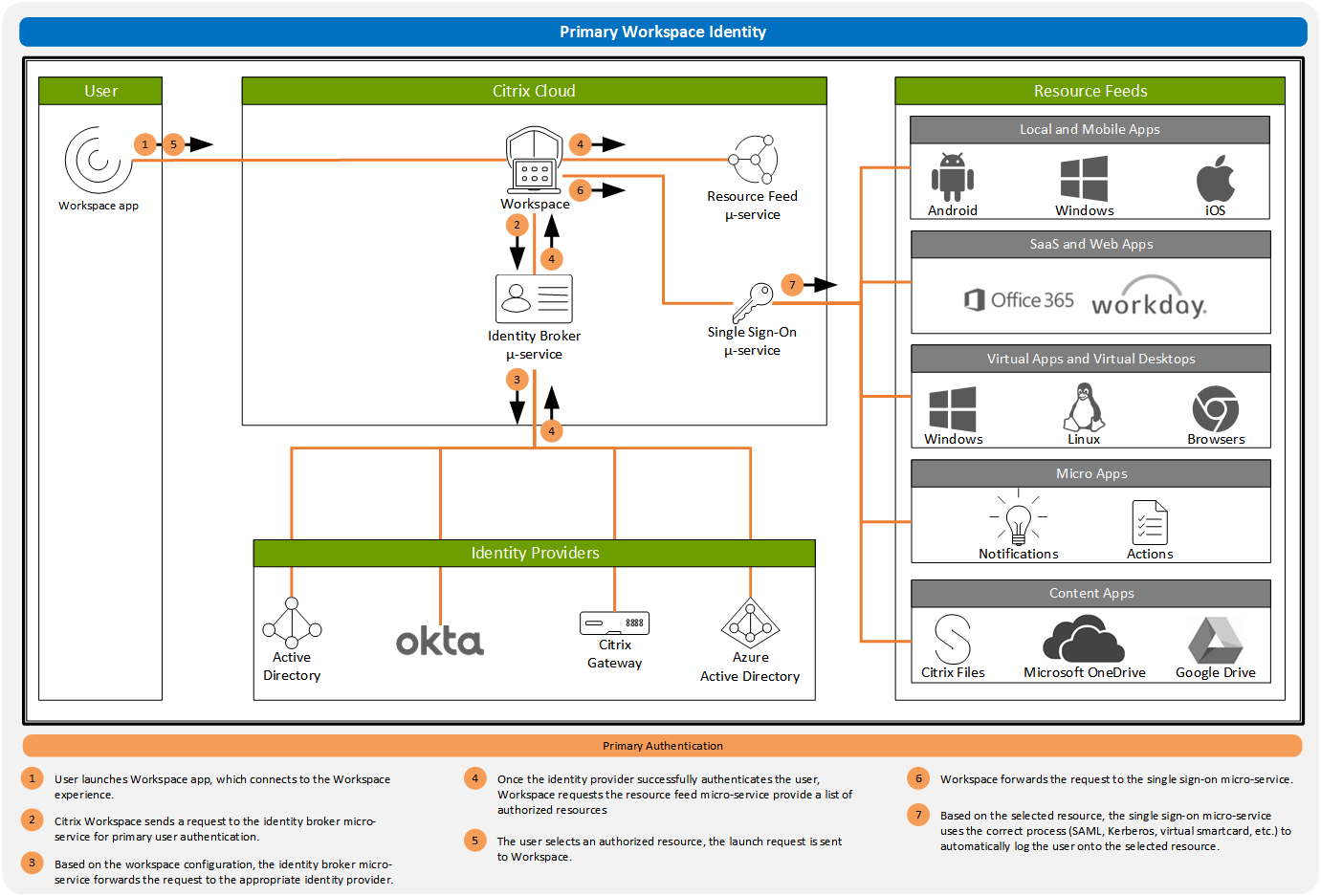
Citrix Netherlands What is single sign-on (SSO)? Single sign-on (SSO) is an authentication capability that lets users access multiple applications with one set of sign-in credentials. Enterprises typically use SSO to provide simpler access to a variety of web, on-premises, and cloud apps for a better user experience.
Installing XenDesktop
Install XenDesktop 7.9 and configure Federated Authentication Service. Refer Citrix Documentation - Federated Authentication Service for more details.
Configuring Active Directory Federation Services (AD FS) and Google Admin Console
Install and configure Active Directory Federation Service (AD FS) from server manager roles on any Windows 2K8 R2 or Windows 2K12 R2 server. Ensure that, AD FS and AD are not on the same machine.
Configure AD FS URL in Google Admin console for Single Sign-on as follows:
Enable Single Sign-on in Google Apps. Log in to your administration console at
http://www.google.com/a/your-domain/. Click Security->Set up Single Sign-on (SSO)This will take you through to a configuration screen. Select Enable Single Sign-on,
and enter the following values:
Sign-in page URL: https://adfs.yourdomain.com/adfs/ls/
Sign-out page URL: https://adfs.yourdomain.com/adfs/ls/
Change password URL: https://sts.yourdomain.com/startersts/users/password.aspxVerification certificate: Upload the AD FS Token Signing cert (.cer file) which can be obtained from the AD FS 2.0 Management Console (under Service > Certificates). Click Upload.
Select “Use a domain specific issuer”.
Enter network addresses in the Network masks textbox.
Single sign-on is configured and enabled. Note that the settings take effect immediately. However, it does not affect your login to the Admin Console – that is always accessed by manual login, so that you can get and disable Single Sign-on again.
Configure SAML Single Sign-on policies on Google Admin Console, refer https://support.google.com/chrome/a/answer/6060880 for more details.
Configuring AD FS
• Open the AD FS 2.0 Management Console and navigate to Relying Parties section.Click Add Relying Party Trust
Choose Enter data about the relying party manually
Provide a name for the trust (so that you can easily identify it)
Select AD FS 2.0 profile
Select Enable support for the SAML 2.0 WebSSO protocol and enter /acs'>https://www.google.com/a//acs in the Relying party SAML 2.0 SSO service URL textbox.
Enter google.com/a/<your-domains the Relying party identifier
Complete the wizard steps
Click on the newly added item and select Properties. Click on the Signature tab and Click Add:
Add the Token Signing Certificate – it must the AD FS Token Signing Certificate you uploaded to the Google Admin Console AD FS.
Click OK.
Click Edit Claim Rules and click Add Rule:
From the Claim rule drop-down, select Transform an Incoming Claim.
Provide a Name to the rule, select E-Mail Address as the Incoming Claim Type, set the Outgoing claim type to Name ID and the Outgoing name ID format to Email:
Complete the Wizard steps.
Go to your Active Directory. Go to properties of user for whom you want to enable Single sign on and then add the google domain email address of that user in Email field.
Go to your Active Directory. Go to properties of user for whom you want to enable Single sign on and then add the google domain email address of that user in Email field.
Configuring Citrix NetScaler
Single Sign On Solutions
- Configure NetScaler SAML to work with AD FS. Before this make sure, XenDesktop works with NetScaler without SSON or FAS configuration.. Refer, http://support.citrix.com/article/CTX133919 to configure NetScaler SAML with AD FS
- On successful completion of all the above steps, you are redirected to AD FS page on entering the SF URL
Configuring Single Sign-on on Chromebook
Citrix Network Provider Order
- Chromebook should be a managed Chromebook
- Install and configure SAML SSO for Chrome app extension on Chrome devices. Refer to the Google website for more information. This extension retrieves SAML cookies from browser and provides to Citrix Receiver. This extension needs to be configured with the following policy to allow Receiver to get SAML cookies:
{
'whitelist' : {
'Value' : [
{
'appId' : 'haiffjcadagjlijoggckpgfnoeiflnem',
'domain' : 'saml.yourcompany.com'
}
]
}
} - If you are repackaging Citrix Receiver for Chrome, change the appId. In addition, change the domain to your company's SAML IdP domain.
- Configure Receiver to user NetScaler Gateway configured for SAML logon. This enables users to use the NetScaler Gateway configured for SAML logon.
- Login to Chromebook using managed user which will redirect you to AD FS page for the first time. user has to enter the password twice for the first time.
- After successful login, you can access the XenDesktop resources without having to re-enter the credentials. providing any credentials.
Applicable Products
- Receiver for Windows
- Single Sign-on
Citrix Receiver Single Sign On Command Line
Objective
Instructions
To switch on the logging requires an administrator to change registry values where Receiver (with SSON enabled) is installed .Use the following steps:

 1) Navigate to registry path
1) Navigate to registry path Citrix Receiver Enable Single Sign On
- For 32 bit platforms, the registry path is
- For 64 bit platforms, the registry path is
2) Add new String value 'DebugEnabled'='true'
3) Add another String value 'LogPath'=<specify the path to save logs>
Disclaimer
